Must complete 90 credits in major before taking this course.
Defend the Digital World with Advanced Cybersecurity Skills
As cyber threats escalate across all sectors, the demand for skilled cybersecurity professionals is at an all-time high. Our online cybersecurity degree provides hands-on, problem-solving education designed to meet industry needs. This program equips you with essential skills in intrusion detection, ethical hacking, digital forensics, and network security to advance your career in this critical field.
- Finish your program faster with credit for prior learning and experience.
- Differentiate your degree and get your resume noticed with an added certificate. Speak with your advisor for information.
- Consider a career using the skills you learn in this degree.
Building Cyber Defenders for the Future
- Comprehensive Cybersecurity Training: Gain practical skills across intrusion detection, ethical hacking, database management, and digital forensics to tackle real-world cybersecurity challenges.
- Cutting-Edge Technical Skills: Master over 31 essential applications, platforms, and programming languages critical for today’s cybersecurity environments.
- Real-World Application: Engage in hands-on, virtual labs that mirror industry scenarios, ensuring you're prepared to protect digital assets effectively.
- Network and Career Growth: Join a global network of Champlain cybersecurity alumni and connect with industry-experienced faculty, setting you up for a successful career in cybersecurity.
A Nationally Recognized Leader in Cybersecurity
Champlain is a nationally recognized leader in cybersecurity and digital forensics education and home of the Senator Patrick Leahy Center for Digital Investigation & Cybersecurity. With a robust faculty of expert-practitioner instructors who have significant experience working for top organizations and are sought-after thought leaders in the field, we specialize in building agile cybersecurity and digital forensics programs that the meet mission-critical needs of today's businesses, nonprofit organizations, law enforcement, and state and federal governments.
Champlain has been designated a National Center of Academic Excellence in Cyber Defense Education by the U.S. National Security Agency and the Department of Homeland Security since 2006, and Champlain cybersecurity programs have been named best in the nation by SC Magazine. Champlain was also designated as a National Center of Digital Forensics Academic Excellence by the Defense Cyber Crime Center (DC3) Air Force Office of Special Investigations - the fifth college in the nation to receive this distinction - until the program was paused by the Federal Government in Sept. 2025.
Program Curriculum
Champlain's online cyber-security degree course portfolio encompasses the critical skills needed by today's cybersecurity professionals. Graduates of the program are required to complete the following courses.
- Professional Courses (60 credits)
- General Education Courses (42 credits)
- Technical Electives (12 credits)
- General Electives (6 credits)
Total Credits: 120*
* Actual total credits will depend upon the number of transfer credits accepted. Please visit the Transfer Credit Options page for more information.
Note: Some of the courses in this program are available in 15-week terms only. Please contact your advisor for details and information on how this may impact your time to completion.
>> Speak with an advisor to learn more about this program, call 802-357-5188 or complete the form below.
This course provides students with an understanding of the many different devices and technologies, from historical to emerging, that are required to design and build networks. In a broad survey of concepts and terminology, students will learn about topology, communications, protocols, and security, and to diagram basic networks to specification.
From day one, students in this course are problem solving, first in terms of algorithmic design and then as early as week two via programming in the latest version of Python, using PyCharm. Students begin by writing a program to have a conversation, having strings and numbers as input, and advance, by week seven, to building a working password saver program, capable of looking up, adding (and encrypting), and storing passwords.
This course, through guided research and hands-on learning experiences, provides students with an understanding of operating systems, including their core fundamental principles and how they work. Students are introduced to the three most popular operating systems for personal computers (Windows, OSX and Linux), and mobile operating systems, and learn about standard functions such as memory, process/thread, input/output, storage and device management.
Students are presented with the opportunity to expand and showcase their knowledge and abilities in this 15-week course where they are expected to work independently and develop a project related to their major.
Prerequisites
This course is a thorough review of the Transmission Control Protocol/Internet Protocol (TCP/IP) which is used extensively in corporate enterprise networks and the Internet. The course will cover the structure of TCP/IP, its application to data networks, and security issues.
Prerequisites
CMIT-130
This course will introduce foundation subject matter and technologies that are critical to the multidisciplinary landscape of cybersecurity.
This exciting course introduces students to the myriad software tools and best practices for handling digital evidence. Labs utilize Champlain College Online's Forensic VDI and challenge students to begin building their skills, from creating a hash value for a forensic copy with X-Ways Forensics and FTK Imager, to examining evidence with The Sleuth Kit (TSK), Autopsy and/or EnCase.
Prerequisites
Complete CMIT-135 and CMIT-140
Through this course, students learn about what makes up an operating system and the various threats to that operating system and, by extension, the user. The focus of this course is on CentOS Linux and Windows Server.
Prerequisites
Complete CYBR-210.
In CYBR-260, students learn how to script with Python (through IDLE and PyCharm), keeping in sight that being able to program is not just about being able to program. It's also about understanding how programs are put together and how they work, what is possible, and how to control the system.
Prerequisites
Complete CMIT-135.
Cloud computing has become increasingly central to Information Security (IS) strategies both at the corporate and personal level. It unifies a variety of technologies to provide businesses a method to improve business efficiency and reduce costs. This course will cover concepts, protocols and implementation details for working with and implementing cloud technologies within an organization.
Prerequisites
Complete CMIT-130.
In this class, students take an intense look at networks and the ways that we provide appropriate controls and technology to provide security to them, while using Wireshark and NMAP as supporting tools.
Prerequisites
Complete NETW-215.
Mobile devices are convenient, portable, inexpensive, powerful and essential to a lot of people. Considering many people have their own smartphones, it makes sense for some businesses to make use of that by allowing employees to use their smartphones to connect to corporate infrastructure for communication functions. This introduces security issues. Smartphones and tablets are not the only areas where wireless technology introduces risk into the enterprise environment, not to mention putting individuals at risk. Bluetooth, 802.11 wireless networks and near field communications all have the potential to be harmful. This course will cover the risks and remediations associated with wireless technology.
Prerequisites
NETW-210, CYBR-210.
This is a course on how to find and exploit vulnerabilities in systems. While discussing the ethical and legal framework of these activities, students will use Google search techniques (a.k.a. Google Hacking), online applications, including Damn Vulnerable Web Application (DVWA), and Champlain’s virtual environments equipped with Kali Linux, Metasploitable, Nessus, Nexpose, NMAP, Zed Attack Proxy (ZAP), W3AF, Burp, and Security Administrator Tool for Analyzing Networks (a.k.a. SATAN), among other tools.
Prerequisites
Take CMIT-135,WEBD-125 and WEBD-220 or CYBR-210
CYBR-320 covers strategies, techniques and technologies used in attacking and defending information systems, and how to design secure networks and protect against intrusion, malware and other hacker exploits. Students will use the Security Onion Linux distribution and the Security Onion toolkit and will perform some log analysis. However, the course has its bigger focus on best practices.
Prerequisites
CYBR-240, CFDI-240, CYBR-210.
In CYBR-410, students have a look on how the landscape of threats and defenses is evolving. Some of the tools used in the class are: Social Engineer's Toolkit (Kali Linux), Metasploitable, Low Orbit Ion Cannon (loic), hping3, TinyCA, and openSSL.
Prerequisites
CYBR-335, CYBR-210.
This introductory course to Wireless LANs focuses on the design, planning, implementation, operation, and troubleshooting of Wireless LANs. It covers a comprehensive overview of technologies, security, and design best practices with particular emphasis on hands-on skills.
Prerequisites
CMIT-130, CMIT-135
This course examines cybersecurity policy planning in an organizational context. The aim is to examine key procedures, such as security requirements analysis and risk assessments, to determine their roles in policy formation.
Prerequisites
CYBR-335
From storyboard to form creation, students walk through the steps to create a basic four to five-page website to specification in this course that introduces HTML5 and CSS. Hands-on assignments reinforce skills development and best practices in design: navigation, column layout, image editing and usage, fonts and tables.
NETW-255 is a lab-based course designed to introduce system administration in both Windows Server and Linux Server operating systems. Students learn how to install both Linux and Windows Operating systems, configure an Active Directory domain, learn common domain administration tasks, apply user and file management, experience application installation and configuration, and integrate the two operating systems to work together simulating a real-life work scenario.
Prerequisites
Complete CMIT-130 and CMIT-140..
Project Management is the formal application of knowledge, skills, tools, and techniques to project-based activities to meet organizational requirements. Project management is accomplished through the use of processes such as Initiating, Planning, Executing, Monitoring and Controlling, and Closing. Project managers can divide projects into these phases to provide better management control with appropriate links to the ongoing operations of the organization. Collectively, these phases, known as the project life cycle, form the foundation for the practice of project management and are guided by the Body of Knowledge from the Project Management Institute (PMI).
Project schedules allow managers, team members, and stakeholders to track progress, set and manage expectations, communicate, control costs, and collaborate. Tasks and deliverables can be monitored and controlled to ensure timely delivery-and if any delays do occur, project managers can easily gauge their impact and make the necessary adjustments. Central to the schedule is a detailed understanding of the project budget, and working to control costs and manage stakeholder expectations.
In addition to the following requirements, students must also complete 3 Credits of a General Education Elective (Any ARTS, COMM, CRIT, ECON, ENGL, HIST, MATH, PHIL, PSYC, SCIE, SOCI, MKCM 120, CRIM except CRIM-225)
This course introduces students to the foundational concepts needed to communicate effectively in writing for academic study and professional development. Students will also learn to read critically to evaluate an author's message. Students will be introduced to rhetorical modes and their role in the development of written communication. Students will also learn how to use revision strategies to create written communication that meets its intended purpose for its intended audience
This course builds on students' proficiency in the writing process and rhetorical modes to introduce the use of sources in written communication. Students will practice information literacy as they learn to determine information needs from sources, develop effective search strategies, and incorporate sources in written communication, legally and ethically.
Prerequisites
Complete ENGL-100
Starting with a frame of human communication as a dynamic system of interactions in which people make choices that impact their relationships, other people, and themselves, students will define theory-informed communication concepts and processes, and critically examine how they apply to everyday life across a variety of contexts. Students will reflect on how the theory, concepts and processes apply to their own lives in becoming competent communicators who are knowledgeable, skilled, and versatile.
This course examines the principles of effective small group interaction. Students will analyze group development stages and small group roles. They will identify and evaluate communication skills that enhance small group cohesion and problem-solving. Students will explain how conflict affects group processes and compare face-to-face versus digital collaboration environments. These skills prepare students to participate effectively in group settings across academic, professional, and community contexts.
Students will learn and apply critical inquiry skills to analyze persuasive communication created by others and to develop persuasive communication/arguments of their own to solve problems in professional, civic, social, and personal contexts. Specifically, students will learn to recognize fallacies in logic; apply inductive and deductive reasoning strategies to the interpretation and development of persuasive communication; evaluate the validity of sources; and develop logically sound persuasive communication. Students will explore the roles of self-awareness, empathy, and ethics in the context of critical inquiry and the development of arguments.
Prerequisites
Complete ENGL-110.
This course is an historical overview, and examination of the evolution of digital, film, and print media, and their functions. Students will identify and analyze contemporary problems of the media such as the legal, social, economic and psychological implications of their relationships with society. They also will examine the ways in which marketing and PR professionals utilize the mass media channels to reach their intended target audiences.
This course explores the complex and evolving relationship between human beings and technology. Through a multi-disciplinary approach that draws on fields such as sociology, psychology, philosophy, and history, students will examine the ways in which technology has shaped human culture, identity, and values, as well as how humans have influenced and continue to influence the development, adoption and use of technology.
Mathematical reasoning, when applied to everyday and professional lives, has two dimensions: logic for deterministic situations and probabilities for non-deterministic situations. This course aims to help students develop these mathematical reasoning skills.
This course introduces students to basic statistics for data literacy. With a focus on exploring real-world data, students will interpret numerical information and utilize the tools necessary to complete the entire statistical process: designing a study; gathering, organizing, and analyzing sample data; and making inferences about a population. Students will demonstrate data-driven decision-making and effective communication of numerical data.
Introduces students to the biochemistry and physiology of nutrition and exercise. Emphasis will be placed on human body systems such as musculoskeletal, digestive, respiratory and circulatory, and their relationship to nutrition and fitness. Students will also study the biochemistry of energy conversion as it relates to exercise physiology. Laboratory sessions are designed to reinforce, by a hands-on approach, the principles discussed in lecture. Course includes two laboratory hours per week.
Students will develop the ability to apply scientific methods to understand the natural world, to identify scientific aspects of daily life, and to evaluate the quality of scientific information based on its source and the methods used for its generation.
In this course, students will gain an introduction to classical mechanics and learn about motion, force, energy, and momentum. The course covers vectors, scalars, and coordinate systems, as well as kinematics in one and two dimensions, Newton's Laws of Motion, circular motion, and kinetic energy and work. Students also learn about potential energy and energy conservation, collision theory, rotational motion, moment of inertia, torque, rotational dynamics, and angular momentum.
This course will introduce students to major streams of social justice thought, including historical social justice movements, theoretical problems having to do with social equality, personal freedom, marginalization, and stigmatization, and the ways in which civic and professional communities respond to these issues.
With pressure and release, a window opens and closes, recording light on a sensor. The simple action captures the instinct, judgement, and skill of the person behind the lens. This class will begin a study of the art and craft of photography. Students will develop their vision and their understanding of how to achieve it. Solid skills will be learned and many doors will be opened.
A survey of the continuing change experienced in art since the 15th century. Students will examine how an image is achieved as well as the significance of the subject represented. Individual inquiry concerning the nature of art is encouraged.
Students learn to appreciate films through the critical analysis of various elements of mise-en-scene, cinematography, editing and sound. The course introduces the conventions of classical Hollywood cinema, considers the work of one major director (auteur), and surveys selected international and independent films. Students view and discuss films each week.
Students in the course will explore the cultural history of the music genre broadly referred to as rock. Students will explore the social, economic and political contexts that are influenced by and that influenced each style in the United States. By listening, watching, reflecting upon, discussing and writing, students will explore how music takes on meaning, personally, and culturally. Topics and themes include the relationships between and among gospel, country, funk, folk, disco, rap and hip hop; the role of business and technology in those relationships, and political or transgressive elements of rock music.
Specific application of common tools for writing in the working world. Students will be instructed in rhetorical strategies of professional writing including style, report formats, editing, document design, and integration of visual aids. Students will complete a semester-long writing project; oral and written reports associated with the process of problem-solving within the project will be included.
Prerequisites
ENGL-112 or COR-125
Students will learn how to create conditions for successful conflict engagement, a necessary skill for any professional. The course focuses on the foundational capacities to remain calm and connected with oneself and others. In this state students can access helpful ideas and responses and be their best selves regardless of environment. Improving facility for conflict creates stronger relationships and reduces fear. By the end of the course, students will understand that disagreement and difference can become a source of personal and interpersonal growth.
In this course, students will explore and apply writing principles and techniques to effectively interpret and write technical workplace materials. Students will enhance and gain skills to communicate business and technical information by producing instructions, describing processes, applying document design elements, creating and integrating illustrations, researching and writing proposals and formal reports, and presenting content for decision-makers.
This course introduces students to the fundamentals of substantive criminal law. With this foundation for understanding the legal system students will identify the essential elements of crimes, including the criminal act, criminal state of mind, and jurisdiction. They will examine the rationale underlying criminal law, factors affecting criminal responsibility, and legal defenses. By analyzing real-world scenarios, students will develop skills to distinguish lawful from unlawful actions and prepare for advanced studies or careers in criminal justice.
This course focuses on the rules and procedures governing how the American criminal justice system must process individuals suspected, accused, and convicted of law violations.
In this course, students will explore the theory and fundamentals of criminal investigation, emphasizing practical applications for evidence handling and case development. Students will review basic responsibilities of investigators and protocols for report writing, evidence collection, and preparation of cases for trial. The curriculum examines investigative approaches for various crime categories, including violent offenses, property crimes, terrorism, and hate crimes, while introducing comparative perspectives from diverse legal systems.
Prerequisites
Take CRIM-120.
Principles of Economics introduces the fundamental concepts of economics - the study of how people manage resources, and how they react to scarcity. This course focuses on both microeconomics (the behavior of consumers and companies) and macroeconomics (large-scale economic factors such as employment and interest rates), so that you'll gain a broad understanding of how a modern market economy functions, how decisions in business settings are informed by economics, and how economics applies to your everyday life.
Students will study important themes in the social history of the United States since the Civil War. This course allows students to expand their critical thinking skills through an examination of primary and secondary sources. Themes might include: the evolving status of women; the immigrant experience; the concept of the American dream; the paradox of freedom vs. slavery; the minority experience; the tensions between social classes. Students will be evaluated primarily on writing assignments.
In this course, students will explore broad, foundational knowledge in psychology, including its history, major theorists and a survey of psychology subfields such as developmental, cognitive and social psychology. Students will also describe and assess the role of ethics and social responsibility in the study and application of psychological theory and practices.
In this class, students will explore how social relationships, groups, societies and culture develop and change over time. From a sociological theory foundation and employing the sociological imagination, students will examine the impact of social structures, institutions, and systems on individual lives. Students will apply sociological research methods to investigate sociological phenomena in their own lives.
Starting Fall 2026 the following changes will be made to the General Education curriculum:
- New category, Integration: CRIT 100 Mindsets for Modern Learning (3 credits)
- Social Science and Arts & Humanities categories combine, still just 6 credits required.
- General Education Electives: credits increase to 6
Starting Fall 2026 students will:
- Remove Technical Electives category and move those credits to General Electives
- Remove MGMT 260/262 as a requirement
- Remove NETW 255 as a requirement
Professional course credits will go from 60 to 54 credits, and General Electives will go from 12 to 24 credits.
Additional Program Details
Graduates of the cybersecurity bachelor's online degree program will demonstrate the following industry-specific skills, knowledge, and competencies:
- Evaluate the computer network and information security needs of an organization.
- Assess cybersecurity risk management policies to effectively protect an organization's critical information and assets.
- Measure the performance of security systems within an enterprise-level information system.
- Troubleshoot, maintain, and update an enterprise-level information security system.
- Implement continuous network monitoring and provide real-time security solutions.
- Formulate, update, and communicate short- and long-term organizational cybersecurity policies and strategies.
Design your own degree and enhance its value and focus by adding a certificate. Adding a certificate allows you to develop specialized skills, strengthen your résumé, and tailor your education to align with career goals. Choose from the undergraduate or graduate certificates on this page.
Note: To earn a certificate, you must speak with your advisor first. You must be officially enrolled in the certificate program before you complete the required courses in it — coursework completed prior to enrollment cannot be applied later, and certificates may not be added retroactively. Careful planning with an advisor is essential to ensure all policies and timelines are met.
- Acrylic Wifi
- Android x86 Emulator
- Burp
- CentOS Linux
- CSS
- Damn Vulnerable Web Application (DVWA)
- Google Hacking
- Hping3
- HTML5
- IDLE
- Linux Server
- Low Orbit Ion Cannon (loic)
- Metsploitable
- Nessus
- Netsh
- Nexpose
- NMAP
- Open SSL
- PyCharm
- Python
- Security Administrator Tool for Analyzing Networks (SATAN)
- Security Onion
- Social Engineer's Toolkit (Kali Linux)
- TinyCA
- Transmission Control Protocol/Internet Protocol (TCP/IP) Suite
- VMware
- W3AF
- Windows Server
- Wireless LANs
- Wireshark
- Zed Attack Proxy (ZAP)
Students who have earned the CISSP Certification are eligible for transfer credits toward this degree. Please speak to an admission representative or your academic advisor for details.
Our admissions team seeks to admit students who:
- Demonstrate a solid academic foundation - a minimum 2.5 GPA is our recommendation, though exceptions may be made on a case-by-case basis for those who demonstrate a potential for academic success in other ways.
- Possess an aptitude for success in an online learning environment.
- Exhibit the ability to make a positive contribution to the Champlain College Online community.
To learn more about submitting transcripts, or requirements for home-schooled students, those educated abroad or returning students visit our Undergraduate Admissions page.
Our transfer credit evaluation team works hard to ensure you get the transfer credits you deserve, from a variety of sources including prior college credits, work experience and training, military training and experience, and more. Our goal is to help you graduate from Champlain College Online as quickly and affordably as possible. Visit our Transfer Credit Options page to learn more.
Champlain College Online's computer science faculty, led by Department Chair Richard Pickering, are expert practitioners in the field. Their industry expertise ensures that our curriculum is aligned with the needs of employers, and reflects the skills today’s IT systems professionals need for success. Classes led by our seasoned experts will give you real-world insight into the world of information technology, and create a rich community of career-focused learning.
We conduct our courses on Canvas. Within Canvas we house our courses, calendar where you can show all your important deadlines, email so you can contact instructors and classmates easily in one place, and of course our new student hub! To see how our classes work in Canvas, view the short video below. Please feel free to contact your admission advisor with any additional questions.
Tuition & Costs
Online Undergraduate Tuition Fall '25 - Summer '26
Tuition & Costs
Online Undergraduate Tuition Fall '26 - Summer '27
* Alumni is defined, for this tuition rate, as any degree program graduate from Champlain College or Champlain College Online.
** Veteran rate effective Spring 2025, not retroactive
See the undergraduate cost of attendance and fees here
Affordability and Paying For Your Education
We provide a number of options to make your online education affordable, including preferred tuition for alumni, associate degree graduates, community college graduates, and military.
Launch a High-Demand Career in Cybersecurity
With cyber threats intensifying, cybersecurity careers are projected to grow 33% from 2020 to 2030. The median annual salary for information security professionals is $103,590*, reflecting the importance and value of cybersecurity expertise across industries.
A Bachelor of Science in Cybersecurity from Champlain prepares you to defend organizations against cyber threats and opens doors to specialized roles across government, finance, healthcare, and more.
*Source: Bureau of Labor Statistics, 2024
Top Careers for Bachelor’s in Cybersecurity Graduates:
- Incident Responder
- Digital Forensics Specialist
- Vulnerability Assessor
- Penetration Tester
- Security Analyst

Why Champlain
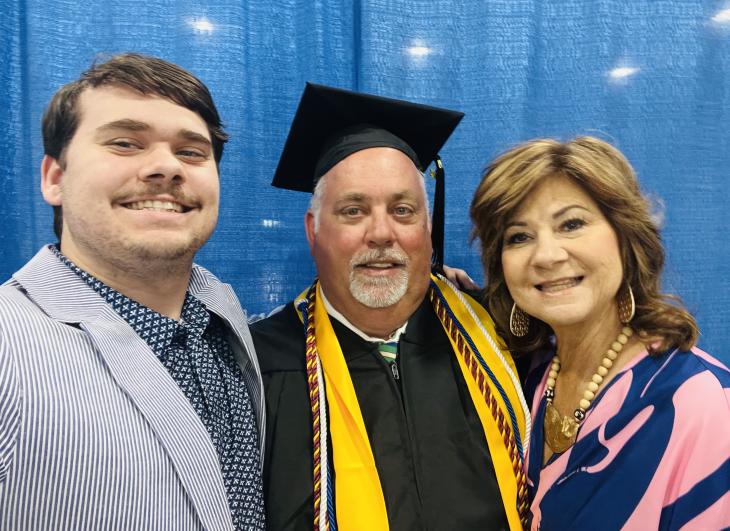
More Than "Just a Grunt"
"30 years is a large gap. All my life I’ve made a living using my hands, physical work, heavy labor, because I honestly thought that’s all I could do. Champlain College…made it easy…and has given me the opportunity to pivot and use something other than my hands. It has taught me that I can use my mind…and I can be someone other than a person that’s just a grunt, a heavy laborer." Watch Tracy's video to hear more from him.
Academic Excellence and Recognition

Regionally accredited by the New England Commission of Higher Education

Designated as a Military Friendly School for our commitment to the military community
Ranked among the best by Tech Guide for game design and computer science

Named the among the best schools with accelerated bachelor's degrees by Intelligent.com
Meet the Program Director
Benjamin Luthy, MS, CISSP, CISM, CDPSE
About
Benjamin Luthy has over 20 years of experience in delivering client-focused technical solutions to safeguard information systems and data in highly regulated environments. He holds multiple industry certifications reflecting his commitment to continuous learning and expertise in security and enterprise technologies. His research interests include information security, intelligence, and cloud computing and traditional infrastructure. As a recognized speaker at industry conferences, he has shared insights on strengthening cyber compliance and has been actively involved in competitive cybersecurity events, including winning the B-Sides Las Vegas Capture the Flag Competition on the 'Joes' team for his work in Windows Operating System Defense.
Outside of his professional pursuits, Ben is a professional musician, enjoys the outdoors, and spending quality time with his family.

Frequently Asked Questions
Cybersecurity can be challenging, but it depends on your background, learning approach, and dedication. With structured learning, hands-on practice, and problem-solving skills, it becomes easier to master. As a nationally recognized leader in cybersecurity education, Champlain College offers renowned faculty and industry-aligned curriculum to help you get the most from your learning – not to mention a flexible, fully online learning format through the BS in Cybersecurity.
A cybersecurity professional is responsible for protecting an organization’s digital assets, networks, and data from cyber threats, such as hackers, malware, and data breaches. You can gain the industry-specific skills and tools you need to protect cyber assets preventively and responsively through the fully online cybersecurity bachelor's degree at Champlain College Online.
A career in cybersecurity requires a mix of technical skills, analytical abilities, and soft skills to protect systems from cyber threats. Learn more about the background you need for this high-impact career here.
A cybersecurity degree can open doors to a wide variety of roles in every major industry. Graduates equipped with this degree can work in roles such as cybersecurity engineer, information security analyst, digital forensics specialist, penetration tester, and many others. You can work in public, private, and non-profit businesses, as well as government agencies, in roles that emphasize protecting data, designing secure systems, or investigating breaches. Because cyber threats evolve constantly, there’s strong growth and demand for skilled professionals. For more info about career outcomes for cybersecurity degree holders, read this helpful article for more details on this topic.
An online cybersecurity degree from Champlain offers the same curriculum, rigor, and accreditation as a traditional program, preparing you for the same certifications and career paths. The difference is in delivery: online students gain flexibility to study from anywhere while completing hands-on work through virtual labs, simulations, and real-world projects. While on-campus programs offer in-person labs and networking opportunities, Champlain’s online format is designed to replicate these experiences and provide strong faculty support. The result is an equally respected degree with added flexibility for working adults.
You May Also Be Interested In
Get Your Cybersecurity Program Guide
Learn what you can expect from our online bachelor's in cybersecurity program.

Download Program Guide
I acknowledge that, by clicking the "submit" button, I am giving my express written consent to Champlain College and its representatives to contact me about educational opportunities via email, text, or phone, at the phone number above, including my mobile phone, using an automatic dialer, or pre-recorded message. Message and data rates may apply. I understand that my consent is not a requirement for enrollment, and I may withdraw my consent at any time.